Built for
Trust
ProofKit generates evidence packages with automatic tampering detection that stand up to regulatory scrutiny. Every PDF comes with protected documents that can't be altered, plus built-in compliance features.
Validation Campaign Status
Real-time verification of ProofKit's algorithm integrity
Validation Campaign: 12/12 Green
Last updated: 2025-08-09 14:32:15 UTC
All validation tests are passing across 6 industries with 12 test scenarios covering PASS, FAIL, ERROR, and INDETERMINATE cases. (INDETERMINATE means we couldn't fully verify the data — usually due to missing sensor readings or data gaps.)
Evidence Verification
Independent verification of ProofKit evidence bundles
For IT teams and auditors — Python Verification Script (Click to expand)
Use this script to independently verify any ProofKit evidence bundle without relying on our servers:
#!/usr/bin/env python3
import json
import hashlib
import zipfile
from pathlib import Path
def verify_evidence_bundle(zip_path):
"""Verify ProofKit evidence bundle integrity."""
with zipfile.ZipFile(zip_path, 'r') as zf:
# Extract and load manifest
manifest_data = json.loads(
zf.read('manifest.json').decode('utf-8')
)
# Verify each file hash
for file_info in manifest_data['files']:
file_data = zf.read(file_info['path'])
calculated_hash = hashlib.sha256(file_data).hexdigest()
if calculated_hash != file_info['sha256']:
return False, f"Hash mismatch: {file_info['path']}"
# Verify root hash
root_hash = manifest_data['root_hash']
file_hashes = [f['sha256'] for f in manifest_data['files']]
calculated_root = hashlib.sha256(
''.join(sorted(file_hashes)).encode()
).hexdigest()
if calculated_root != root_hash:
return False, "Root hash verification failed"
return True, "Evidence bundle verified successfully"
# Usage
result, message = verify_evidence_bundle('evidence.zip')
print(f"Verification: {message}")
This script runs completely offline and doesn't communicate with ProofKit servers, ensuring independent verification of evidence integrity.
For IT teams and auditors — Terminal Commands (Click to expand)
1. Download Evidence Bundle
2. Run Verification
Root hash: 7d41c3f8e6b2a9d5...
Files verified: 5/5
Integrity: PASS
Security Features
Enterprise-grade security for regulatory compliance
Protected Documents That Can't Be Altered
Digital fingerprints that prove nobody changed your data, with a single master code that verifies everything at once.
Long-Term Archive Format
Every report is saved in a long-term archive format (PDF/A-3) so it can be opened and trusted for decades.
Certified Timestamps From a Trusted Authority
Independent, certified timestamps prove exactly when your validation was completed — no one can backdate or alter the time.
Compliance Standards
Meeting regulatory requirements across industries
FDA 21 CFR Part 11
The FDA rule for electronic records in regulated industries.
Covers electronic records and signatures for pharmaceutical and medical device validation.
ISO 13485
The international standard for medical device quality management.
Ensures proper quality management systems for medical devices with comprehensive documentation.
SOC 2 Type II
An independent security audit that proves we protect your data properly.
Covers security and availability controls verified by an external auditor.
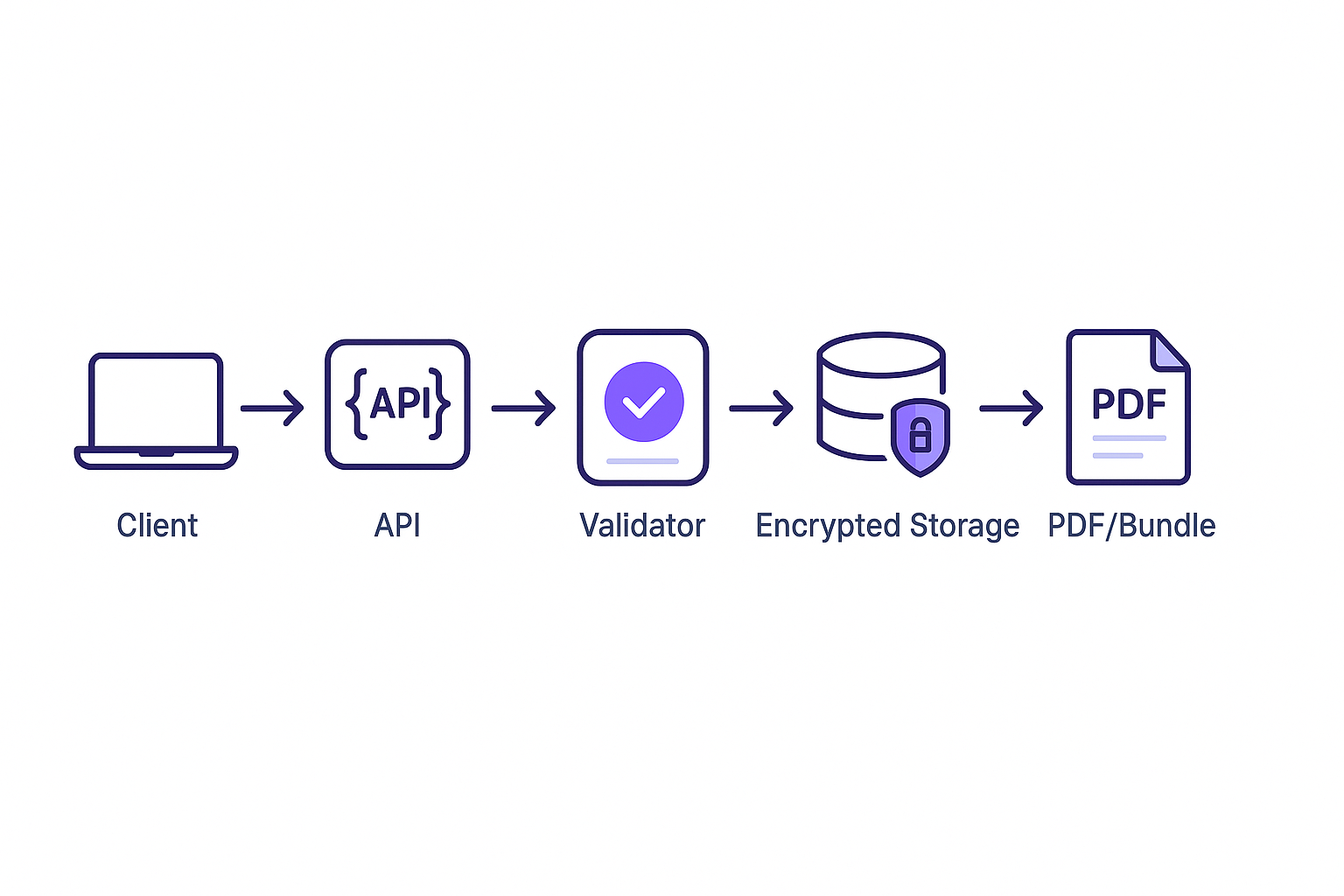
How Verification Works
Simple steps to verify the authenticity of any ProofKit certificate
Quick QR Verification
- Scan QR code on any ProofKit certificate
- Instant verification via our secure verification portal
- View certificate details including timestamps and automatic tampering detection
- Download evidence bundle for complete history of your document
Instant Verification
Every certificate includes a QR code for immediate automatic tampering detection
Quality Assurance Gates
Built-in quality controls ensure certificate reliability
INDETERMINATE Status
What this means: We couldn't fully verify the data — usually due to missing sensor readings or data gaps.
When required sensors are missing or data quality is insufficient, certificates are marked INDETERMINATE and require QA approval before use.
PDF Validation Gates
PDF downloads are blocked if compliance requirements (long-term archive format and certified timestamps from a trusted authority) cannot be met.
Bundle Verification
Evidence bundles include digital fingerprint verification and can be independently checked to confirm nothing was changed.
Enterprise Configuration
Environment variables control compliance enforcement
ENFORCE_PDF_A3=1
Blocks PDF generation if the long-term archive format (PDF/A-3) cannot be applied. Essential for keeping reports readable and legally valid for years to come.
BLOCK_IF_NO_TSA=1
Blocks PDF generation if certified timestamps from a trusted authority are unavailable. Required to prove when validation happened and prevent backdating.
Ready to Build Trust?
Experience ProofKit's security features with your temperature data
Try ProofKit Now →